The Old Stuff bucket
In redoing the site from the crappy olden version, I couldn’t be arsed to bring across these old articles as these projects are abandoned, ancient, unfinished, or all of the above. This post is a home for lost projects.
iGeek, an iPhone ‘geekport’
20th January 2011
I never had a BeBox, but I really liked the Geekport they had. It was a general I/O port, for random hacking projects.
This is an Altoid-tin-housed similar port, portable and iPhone-friendly. With a jailbroken iPhone/iPodTouch/iPad, you can access /dev/tty.iap and easily splat stuff through its dock connector serial port. This is a small board with an ATmega48 uC whose UART interfaces to the dock connector serial pins.
Anyway, again fairly half-finished. It has a 1-wire DS18B20 temperature sensor and pictured is a little test prog on an iPod Touch, dumping the temperature. I have a NES gamepad that plugs into the I/O header too, which the AVR can read. There are I2C, GPIO and ADC pins available…. for portable McGyver (sp) ri0t engineer fun!
Amstrad Emailer E2
29th January 2006
I wrote a crappy yet great boot monitor for the Amstrad E2 Emailer. I got about a billion for 10UKP each at one point — they’ve been long since forgotten by Amstrad. They’re a nice ARM7TDMI board with a great big mono LCD, various I/O and are useful for controlling other things.
If you’ve picked one up, I strongly suggest reading the mailing list archives for info on hacking these machines (if you haven’t already). Another utility, ‘pblq’ is required to reflash the E2.
e2-monitor
This is not a PBL replacement, but is loaded by PBL and replaces the Amstrad firmware. It provides an environment that will simply load a user application and provide some basic services.
Features:
- Peek/poke/dump/fill memory addresses - useful for probing GPIO/peripherals.
- Jump to address - APCS-like call, can be used to do a proper function call & provide arguments.
- XMODEM upload/download - transfers to RAM
- CRC32 of memory blocks
- PBL NAND flash read/write to/from RAM
- Boots from PBL
- Loads/executes subsequent programs from flash
- Basic SWI interface usable from client programs for console I/O
Download e2-monitor v0.26:
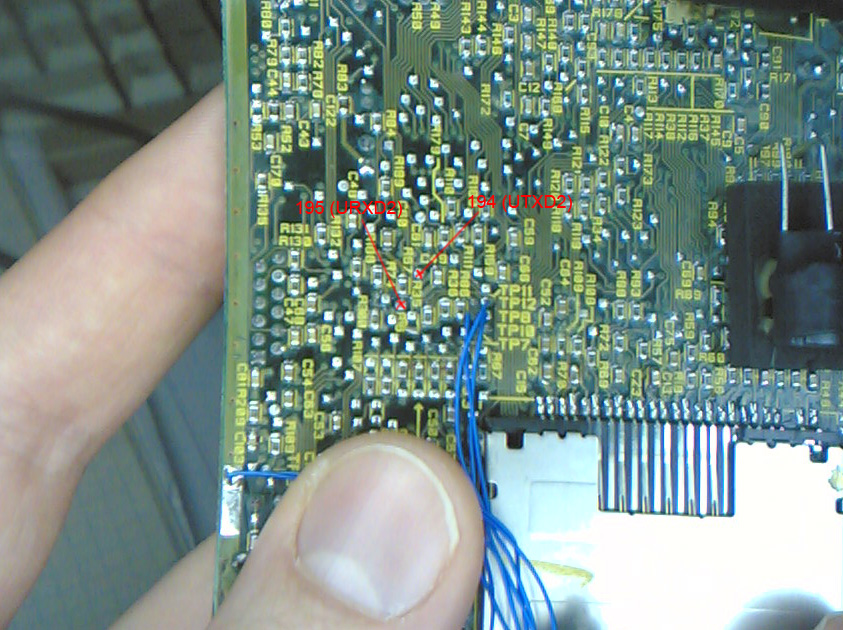
Second UART pads
In addition to the ‘earplug’ serial port, a second UART is available here:
Gameboy Advance projects
1st May 2002
Free, simple, portable GBA Multiboot link cable
This is an 8051-based MBC cable for the GBA. Please see Steve Lynch’s AVR port of this cable code.
The cable interfaces to a PC (or workstation) serial port at 115kbit/s, and contains a DS89c420 microcontroller. The job of this is to accept two bytes from the PC, and send it to the GBA in its weird 16bit serial format. When it receives a reply from the GBA, it is sent back to the PC.
It does more or less the same thing as Jeff Frohwein’s MBC2 cable, and Miguel Angel’s “Intelligent multiboot” cable – formats data from the PC. However, it has an RS232 interface instead of a parallel printer interface. As such, it is more flexible and will run from any machine with any OS (that runs the software ;). The software (currently x86 Linux) simply needs to talk to the serial port, no low-level hacks are needed.
Status:
Reliable operation! Downloads a small 2nd-stage booter from the PC using Miguel’s protocol code, then sets up standard UART communication from the GBA (the cable falls silent and ‘disappears’ from the cable, doing passthrough from GBA to PC); the bootloader then downloads the actual code into IWRAM at the full 115k2bits/s. The download speed is very good, running nearly flat-out.
Schematics and software
A crappy ASCII-art schematic is in the “Matt’s Serial Multiboot Cable” (or MSMC) archive below.
- Download MSMCcable-1.0.tgz (20k).
This code is rather 8051-specific. Please port it to your favourite microcontroller (PIC, AVR, 4040 etc…)!
You may need an 8051 monitor, check out PJRC for PAULMON2.
Firedemo (MattDemo3)
- Download stereo version
- Download mono version (both ~128K)
This has been tested on VisualBoy Advance (with SDL under Linux) and on real hardware (using my MB cable ;) The image is MultiBoot-capable, but should also work from flash.
Two versions are here: the stereo version works great on real GBA hardware, but craply on VisualBoy Advance. Until I find out why, the mono version works OK on the emulator so use that one.
The graphics look a bit strange in the screenshot. To see it moving makes it alllll suddenly make sense…
BushSTB hacks
Circa May 2002
During 2002 whilst I was busy dropping out of my PhD, I started toying with a set-top “Internet TV” box made by Bush/Pace. It’s got an ARM7 in it. After attaching a Sharp LCD panel (with Meccano…) I ported/cleaned up the ethernet driver/IP stack/scheduler that I’d previously hacked up, and made it into a more complete bootloader. The SoC is a Cirrus CL7500FE. The LCD is a Sharp 640x480 9-bit panel that I got surplus for £1. It’s attached to the CL7500FE’s genlock output bus (airwires onto a PQFP208 package).
The contraption contains an ISA NE2000 ethernet card that is driven through the board’s printer port using a custom A/D bus demultiplexer board, and the bootloader brings in a kernel using TFTP. I’d got to the point where I had a dodgy Linux 2.4 port running on it, but didn’t really use it for much.


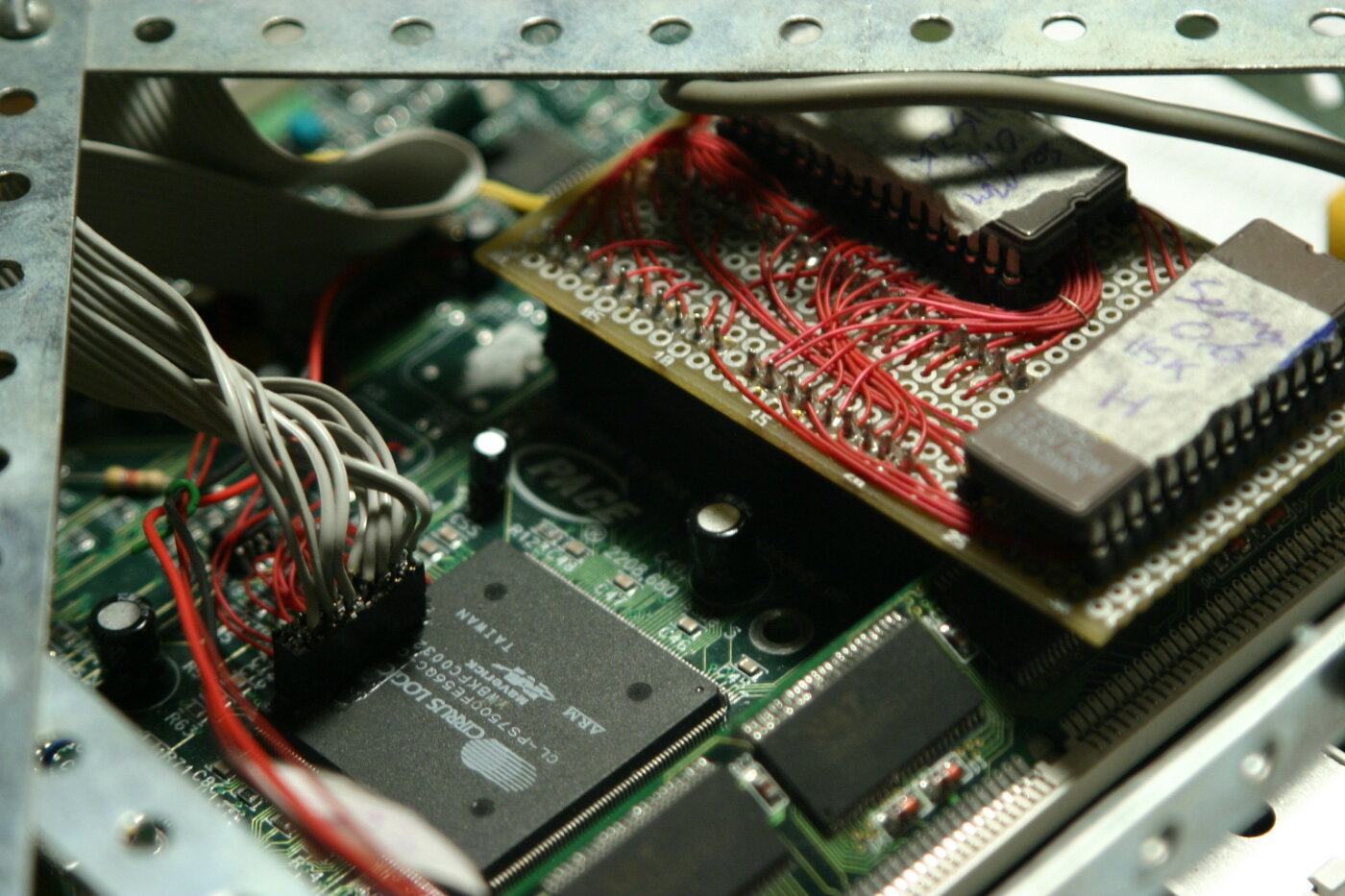
The firmware is 100% ARM assembler and implements a basic thread scheduler, locking/queueing primitives, basic memory management, an NE2000 driver, ARP, UDP, IP and TFTP. The firmware is stored in two actual EPROMs. Yes, code, burn, debug, erase, code, burn, debug, kebab, erase, etc.
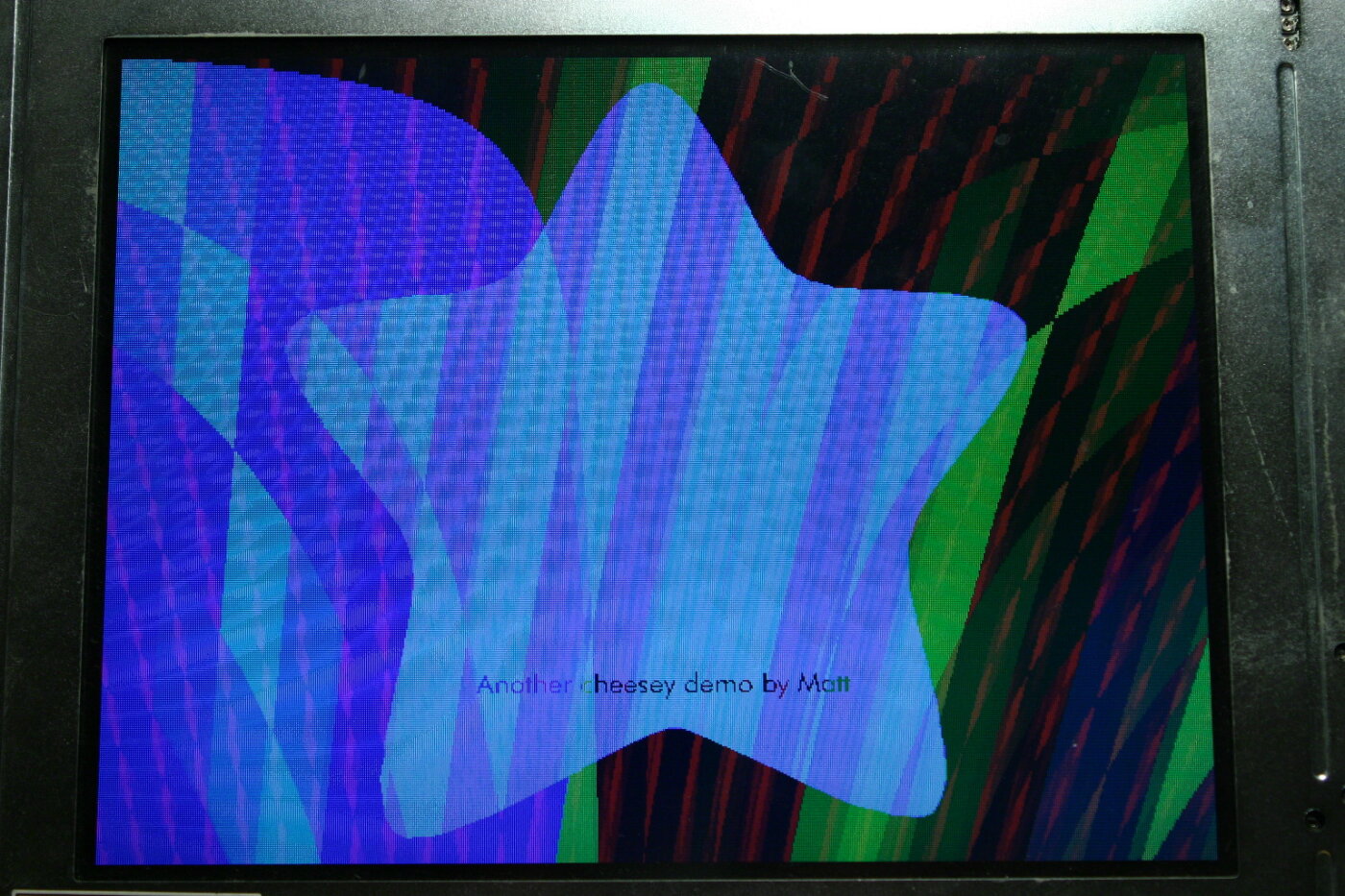
The bootloader implements a basic serial shell to configure the bootserver and filenames, details of which are stored in the board’s EEPROM. Below it’s running a couple of swirly animated demos:
There are no applications for this. It just twirls about, it’s not amazingly useful. It almost fits on the wall… to make a garish addition to any modern livingroom!
See also Vincent S’s STB hacking page.